Encryption¶
Warning
If you already use a sysPass version <= 2.0, it’s advisable to update to 2.1 version and then to 3.1, in order to use the new security improvements on the encryption mechanisms (CVE-2017-5999). Please see Updating for upgrading details.
sysPass encryption is based on AES-256 in CTR mode by using PHP’s OpenSSL module. It uses the Defuse/php-encryption library for the encryption modules and functions management.
The encrypted data (up to 3.1 version) are:
- Accounts’ passwords (always)
- Accounts’ public links (always)
- Custom fields’ data (if set)
- Plugins’ data
- sysPass XML format export (if set)
- PHP’s session data (if set)
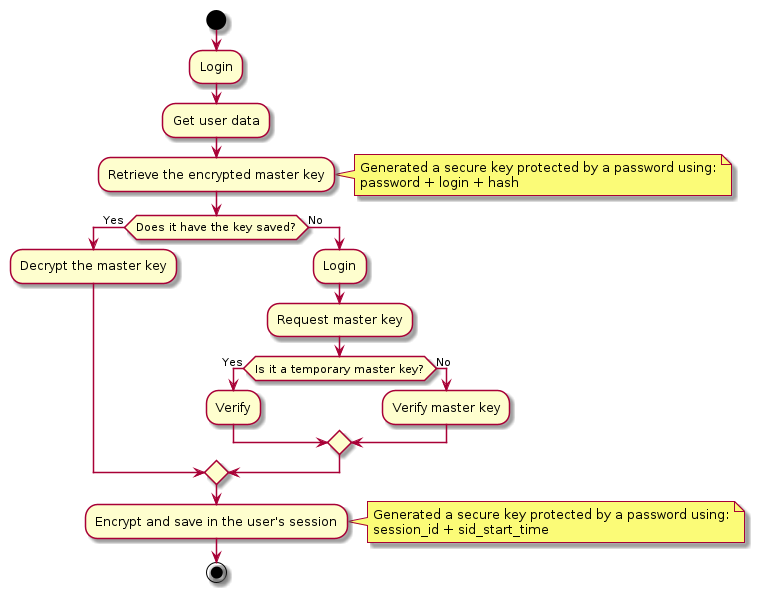
In order to use the application, for every user first login, either a master password or a temporary master key (see Temporary Master Key) will be needed. That is so because the master password is not stored in the web server but a a generated Blowfish hash is saved in order to check if the user is using the correct master password.
After logging in with the master password, it’s encrypted and stored within the user’s data in the database. The encryption key is generated using a derived key from user’s password and login, and a secure random salt generated by openssl_random_pseudo_bytes (stored in “…/app/config/config.xml” file).
On next user logins the master password is got from the user’s data and decrypted by using the derived key. After this, the master password is encrypted again for storing it in the user’s PHP session, so every time the master password is needed it must be decrypted using a session-based generated key. This key is regenerated every 120 seconds.
The master password will be prompted again if:
- The user changes either its login password or username. The previous password will be requested.
- It has been changed by the administrator.
- The configuration salt is changed.
Note
A temporary master key (see Temporary Master Key) could be used instead of the real master password
Temporary Master Key¶
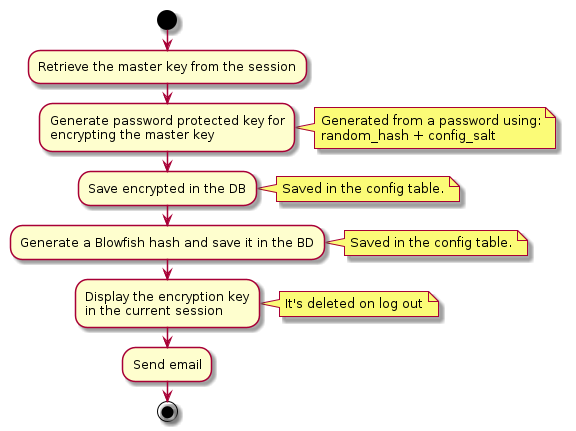
A temporary master key could be generated to be used by the application users, so it won’t be needed to tell the real master password.
For the temporary master key generation the real master password is encrypted using a secure key generated by openssl_random_pseudo_bytes. Then a Blowfish generated hash of it is stored in the database “”Config” table.” in order to check it when the temporary master key is provided on login.
Note
The real master password is never stored unencrypted. For checking the temporary master key, a Blowfish generated hash is only used
PKI-RSA¶
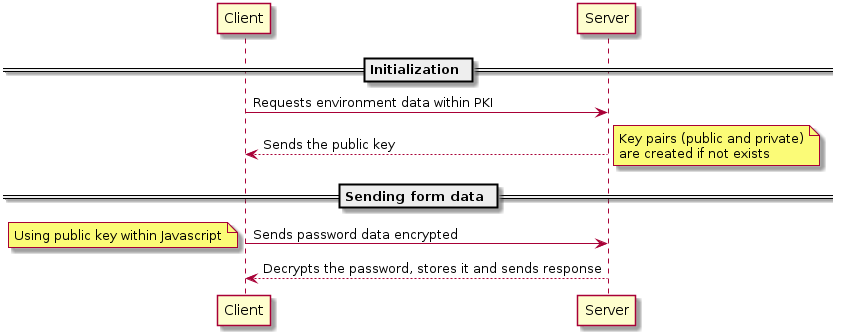
In order to improve the security of the sent data, RSA (PKI) is being used for encrypting the passwords that are being sent from the application forms. This prevents to send sensitive date through plain channels.
Public and private RSA keys are generated within the application “…/app/config” directory.
Note
Data flowing from server to client side is not encrypted unless you run over an HTTPS channel.
Diagrams¶
Login Process¶
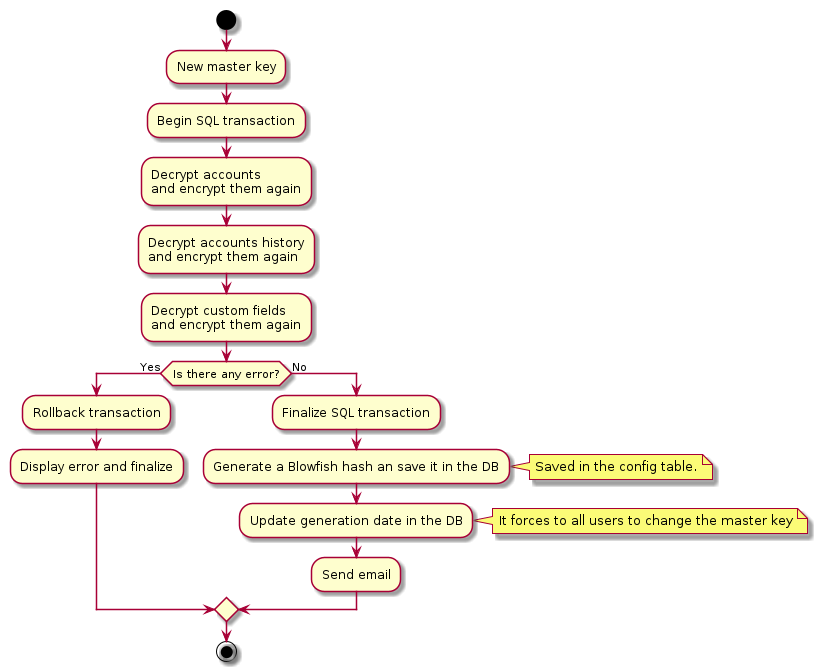
Master Password Process¶
Temporary Master Key Process¶
PKI Process¶
Warning
Be aware that the highest security risk is in the users themselves, because a compromised password could cause a security leak.
A sysPass compromised server could be dangerous if the database is placed alongside the web server, because the network data could be sniffed so the passwords would be revealed.